Overview
Once every true-linux engineer gets a trouble: there is no any software in his distro or it's built without needed options. I am keen on the phrase: "Only source control gives you freedom".
Of course, you can build this software on your computer without any src-packages, directly (with simplification: configure, make, make install). But it's a non-reproducible solution, also hard for distribution.
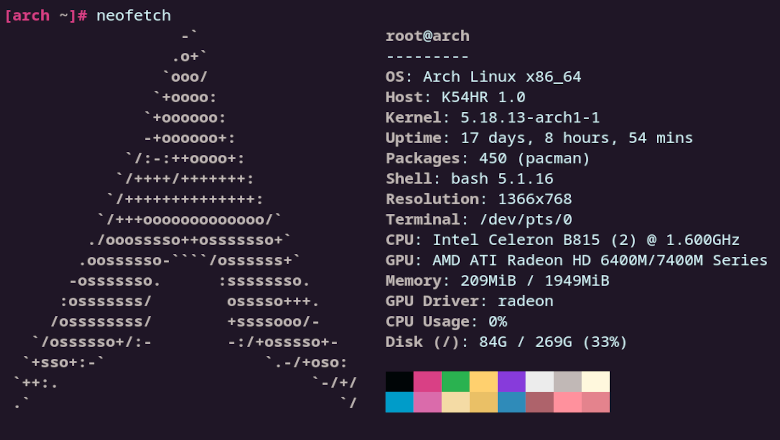
The better way is to make distro-aligned package that can be built if needed and that produces lightly distributed binary-packages. It's about debian-source packages(debian,ubuntu,etc), pkgbuild (for arch), ebuild for gentoo, src-rpm for red hat-based, and many others.
I will use cri-o like a specimen.
Before reading the text below I strongly recommend to get familiarized with the official Debian policy manual placed here and debhelper manpage.
Also you will be required to setup some variables like DEBMAIL and DEBFULLNAME for proper data in changelog and other places.